Brave the Unknown: Confronting Hidden Threats with Confidence
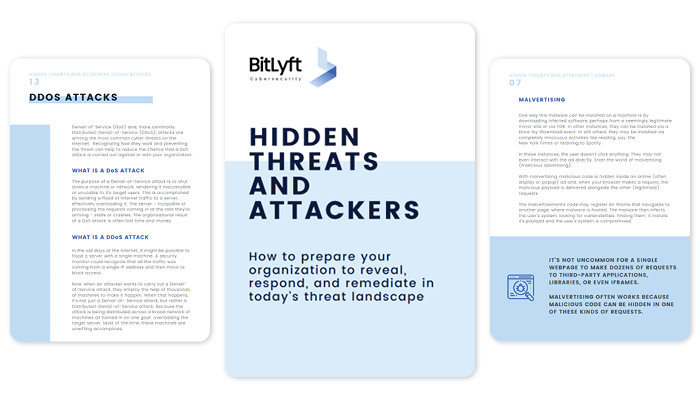
Navigating the murky waters of cybersecurity can be daunting. Invisible threats lurk in the depths, putting your business's reputation and financial stability at risk. Our free guide, "Hidden Threats and Cyber Attacks," throws light on these shadows, revealing insidious cyber threats like fileless malware, living-off-the-land attacks, and zero-day exploits, and shows you how to counter them effectively.
Do you know what's lurking in your network?
Hidden threats are a growing concern for businesses. They can cause data breaches, unauthorized access, and damage to reputation and financial stability. In this free guide, learn how to reveal and respond to some of the hardest to detect cyber attacks.
Learn the importance of adopting advanced security measures, like behavior-based detection and response, network segmentation, and endpoint detection and response (EDR).
Get recommendations for conducting regular security assessments and tests to identify and address vulnerabilities in the IT environment.
Discover the importance of adopting a multi-layered security approach to protect against hidden threats and safeguard critical assets and data.
Get tactical advice for combatting some of the most common hidden threats like fileless malware, LOTL attacks, and zero-day exploits
FAQs:
Who is this guide for?
IT professionals seeking to understand and combat hidden cyber threats.
How will this guide help me?
It provides actionable insights to help you safeguard your critical assets.
Is it really free?
Absolutely! Our aim is to equip businesses with the knowledge they need to stay safe.
Knowledge is power.
Download "Hidden Threats and Cyber Attacks" now to empower your business with a fortified defense strategy

